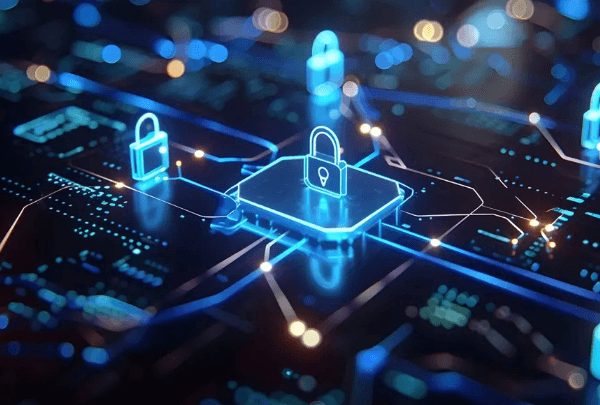
Digital security logs are crucial for monitoring system activities and detecting threats. The 8x7x6x5x4x3x2x1 framework emphasizes a structured approach to logging and alerting. By capturing comprehensive data, organizations can ensure compliance and enhance their security measures. However, the effectiveness of these logs depends on their analysis and response strategies. Understanding how to prioritize alerts can significantly impact security outcomes. What are the best practices for maintaining these logs effectively?
Understanding Digital Security Logs
Although digital security logs may seem like mere records of activity, they serve as crucial components in the overall framework of cybersecurity management.
Log retention policies dictate how long these logs are stored, impacting analysis and compliance. Moreover, diverse log formats facilitate various data types, enhancing the ability to identify anomalies.
Understanding these elements is essential for maintaining robust security postures and ensuring operational freedom.
Key Components of Effective Logging
Effective logging is underpinned by several key components that enhance the utility and reliability of digital security logs.
Log retention policies ensure that essential data remains accessible for analysis over time, while log integrity mechanisms safeguard the accuracy and authenticity of the records.
Together, these elements foster a robust logging framework, enabling organizations to maintain security and compliance in a digital environment.
Analyzing and Responding to Alerts
The reliability of digital security logs is not only determined by their creation but also by the processes involved in analyzing and responding to alerts generated from these logs.
Alert prioritization is crucial for effective incident response, ensuring that the most critical threats are addressed promptly.
This structured approach enhances security posture, allowing organizations to mitigate risks and maintain operational integrity while safeguarding individual freedoms.
Best Practices for Maintaining Security Logs
Establishing robust practices for maintaining security logs is essential for ensuring data integrity and compliance.
Effective log retention policies should dictate the duration for which logs are stored, balancing regulatory requirements and storage capabilities.
Additionally, regular audits enhance log integrity by identifying discrepancies.
Employing encryption and access controls further protects logs, ensuring they remain tamper-proof and accessible only to authorized personnel, thereby safeguarding critical information.
Conclusion
In the intricate tapestry of digital security, logs serve as the vigilant sentinels guarding the castle walls. Each entry, like a thread, weaves together a narrative of activity and alertness, revealing potential threats lurking in the shadows. By adhering to best practices in log management, organizations fortify their defenses, ensuring that the fortress remains intact against the relentless tide of cyber adversaries. Ultimately, effective logging is not merely a safeguard; it is the backbone of resilient cybersecurity.